One of the features that I have found missing in StoreFront is the ability to set different timeouts for different categories of users. For example, you may wish to have a shorter timeout for users in a sensitive department (e.g. Finance). If you feel the same way, read on ...
Let's assume that you would like the Finance department to have a shorter timeout period (e.g. 5 minutes) rather than the default value of 20 minutes. First, you would need a way to determine if the user logging on to StoreFront is in the Finance department. You would then need to set the appropriate timeout based on the user's membership.
The first requirement may be accomplished by adding the following .Net .aspx file (inGroup.aspx) to the custom directory. You pass it the user's ID and the department (OU) you wish to check for membership. and it will return true if the user is a member of that OU or false if the user is not. It is beyond the scope of this post to explain each of the routines in the file, but two points need to be mentioned.
1) You must edit the file at line #11 to reflect the user root OU and your company's domain:
string rootOU = "OU=Accounts,DC=domain,DC=com";
2) You need to add an assembly to the file web.config in your store's web directory (e.g. /Citrix/StoreWeb). To do this:
- make a backup of the web.config file.
- open the file and search for <assemblies>
<assemblies>
<add assembly="System.Web.Mvc, Culture=neutral, PublicKeyToken=31BF3856AD364E35" />
<add assembly="System.Web.Abstractions, Version=4.0.0.0, Culture=neutral, PublicKeyToken=31BF3856AD364E35" />
<add assembly="System.Web.Routing, Version=4.0.0.0, Culture=neutral, PublicKeyToken=31BF3856AD364E35" />
</assemblies>
- insert the following line right before the closing </assemblies> tag
<add assembly="System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a" />
- which should then look like
<assemblies>
<add assembly="System.Web.Mvc, Culture=neutral, PublicKeyToken=31BF3856AD364E35" />
<add assembly="System.Web.Abstractions, Version=4.0.0.0, Culture=neutral, PublicKeyToken=31BF3856AD364E35" />
<add assembly="System.Web.Routing, Version=4.0.0.0, Culture=neutral, PublicKeyToken=31BF3856AD364E35" />
<add assembly="System.DirectoryServices, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a" />
</assemblies>
- save the file
You also need to copy the contents of this script file (script.js) into the script file currently in the custom directory (after backing it up, of course). At the very top of the file you will see:
// group to get a special timeout
var specialGroup = "Finance";
var specialTimeoutMins = 5;
You will need to modify the above for the AD group to check for and the special timeout (in minutes) for that group.
Note: You need to make sure that the timeout specified in your StoreFront configuration is greater than your special timeout, or StoreFront will log you out before you reach your custom timeout.
The JavaScript code sets a timer based on the timeout value specified and simulates a click on the logoff link when the timer expires.
function logout() {
log("Session timeout has expired ... logging out ... ");
$('#dropdownLogOffBtn').click();
}
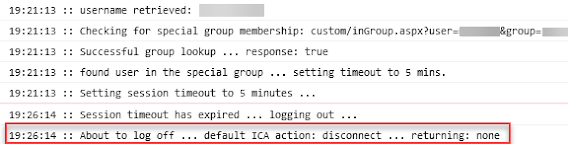
Logging code has been added to the above which you can view by activating the console in your browser's Developer Tools. Here is a sample of what you would see if the user is in the special group:
Here is a sample of what you would see if the user is NOT in the special group: